Gluware is a Bain Capital Portfolio Company
- IndustriesINDUSTRIESABOUT
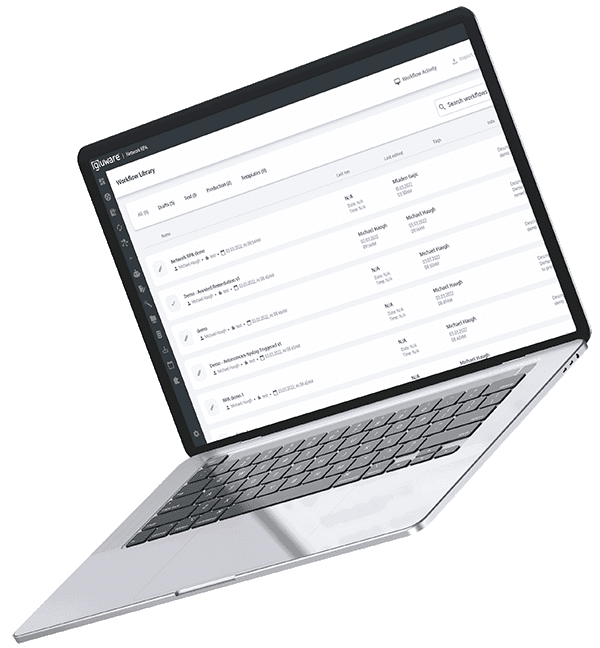
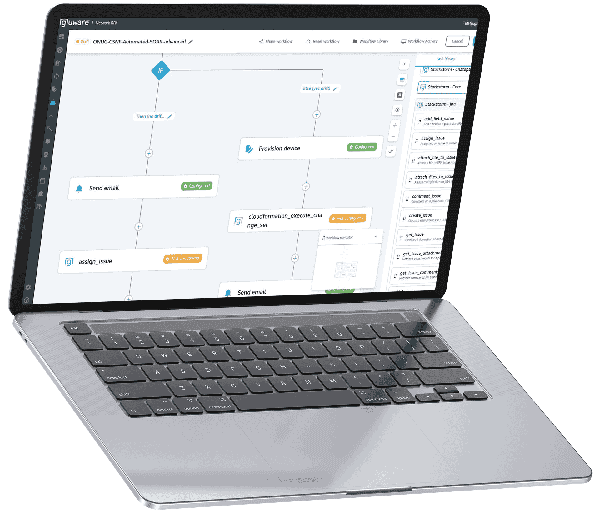
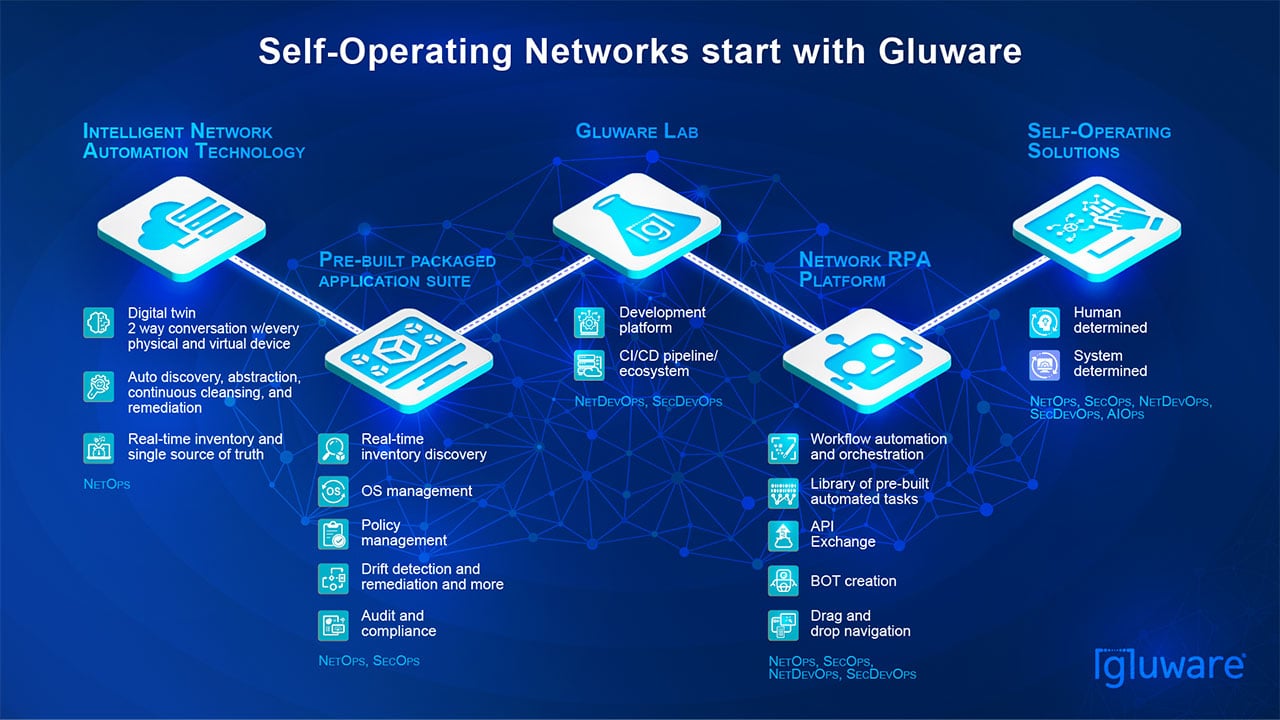
Every day, Gluware helps leaders across industry automate network configuration changes, perform OS upgrades at scale, and conduct recurring audit / compliance checks and remediation, resulting in significant time and cost savings.
- Intelligent by Design
- ProductsAPPLICATIONS / SOLUTIONS
- PartnersGLUWARE PARTNERSBECOME A PARTNER
Gluware partners with the world’s leading technology companies and resellers to deliver a wide array of solutions built around our industry-leading network automation platform.
DEAL REGISTRATIONGluware partners/resellers can register new account opportunities.
- Customers
- Resources
- CompanyABOUT GLUWARENEWSROOMEVENTSCONTACT US
Gluware, Inc.
2020 L Street
Suite 130
Sacramento, CA 958111-916-877-8224
sales@gluware.comFor general inquiries info@gluware.com
SUPPORTsupport.gluware.com
support@gluware.comUS: 1-855-458-3822
UK: 0808-134-9906
Netherlands: 0-800-023-2194
Australia: 1-800-987-824
NZ + 0800-005-106